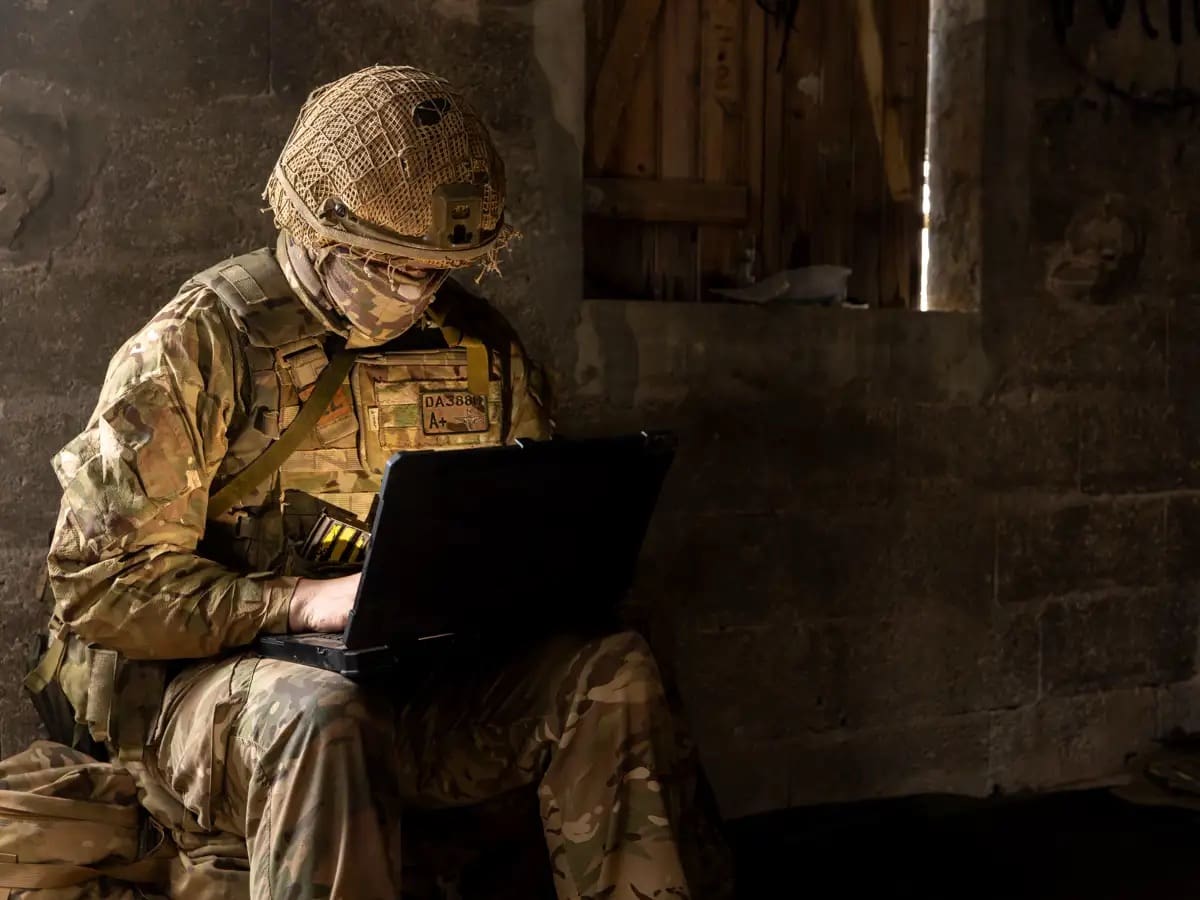
To survive on the modern battlefield, paratroopers are adapting to fight the unseen battle on the radio waves.
Phantom Platoon provides a unique Cyber and Electromagnetic Activities (CEMA) capability for 16 Air Assault Brigade, the British Army’s global response force.

CEMA brings together electronic warfare, cyber operations, and spectrum management. The goal is to gather information about the enemy, disrupt their plans, and keep friendly forces safe.
The platoon – part of 2nd Battalion The Parachute Regiment (2 PARA) – took part in Exercise Orion in France, where British and French airborne soldiers trained side by side to prepare for real-world crises.
Building their own kit
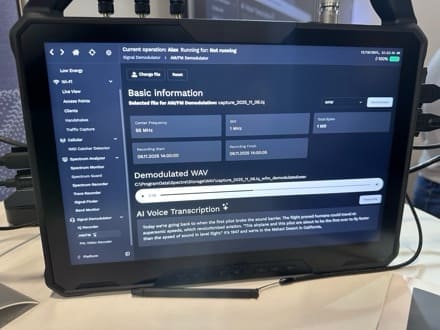
A key task for the CEMA specialists was to find enemy positions by tracking their radio transmissions. The soldiers used Kraken, a software defined radio they have put together themselves.
“It’s an aerial to detect signals that links to a GPS, and is run through a single-board computer,” Private Kai said. “It takes five minutes to set up or take down, and we can position it on the battlefield and connect remotely from anywhere.
“When we track a signal and detect what and where it is, that goes towards building up a picture of the enemy and what they are doing.”
Other devices the paratroopers have produced are the Unagi, a transmitter that can jam radio signals or send out fake ones; and the Plankton, a Wi-Fi extender used to cut the signal between a drone and its controller.
Private George said: “One of our team has a degree in marine biology, so everything we do has some kind of fishy name! We make our kit with components bought at an electronics shop and, with a quick bit of coding, we can reprogramme a device to deliver a different effect.
“We were using Unagi to jam radios, and then we reconfigured it to mimic a Wi-Fi hub. The enemy picked up that signal and thought they had located our headquarters, so they attacked that fake position. Deceiving the enemy meant one of our rifle companies seized their objective without any opposition.”

Why this matters
Private Kai said Phantom Platoon’s work was an example of “the airborne initiative”.
“As paratroopers we want to be the best and win every fight,” he said. “Looking at fighting around the world now, electronic warfare is playing a big part – we’ve seen that and created this capability for ourselves.”
For Private George, CEMA has brought a childhood interest in electronics into his military career.
“I grew up playing PlayStation and Xbox, and then started messing around with the hardware,” he said. “When I first heard about CEMA, I was really keen to get involved. I enjoy working on electronics out in the cold and wet, and I get a real sense of how my skills can make a difference.”
2 PARA’s commanding officer Lieutenant Colonel Craig Shephard said: “CEMA is about finding out what the enemy is doing and creating confusion about our actions and intentions. By doing that we aim to gain that small advantage in time or space needed to win the battle.
“The work of Phantom Platoon shows the real willingness among paratroopers to innovate and adapt to the modern battlefield. That enthusiasm, and the capability it has created, is a fantastic asset to have as a commander.”
Exercise Orion brought together 2,000 soldiers from 16 Air Assault Brigade and France’s 11e Brigade Parachutiste to train to conduct defensive operations. As the Airborne Combined Joint Force, the two brigades have been trained and ready to deploy together in response to global crises since 2013.
Via UK MOD
MOD Crown Copyright